For years, enterprises have taken advantage of remote access VPNs to ensure the secure availability of resources, and for many people, the phrases “remote access” and “VPN” are synonymous. However, enterprises are rapidly adopting cloud applications and given the recent surge in remote working, network and security teams are struggling to keep control. Having so much data routed through central hubs is creating data bottlenecks when large numbers of employees are all attempting to access the information they need.
Considering these new requirements, is remote access VPN still relevant today, or is it time to find a better architecture?
Limitations of Remote Access
Remote access acts as a gateway to allow users past the perimeter firewall to access resources in the data centre and now so many more of us are having to leverage remote access from home, your network edge has ballooned dramatically, emphasising the limitations of VPNs at large.
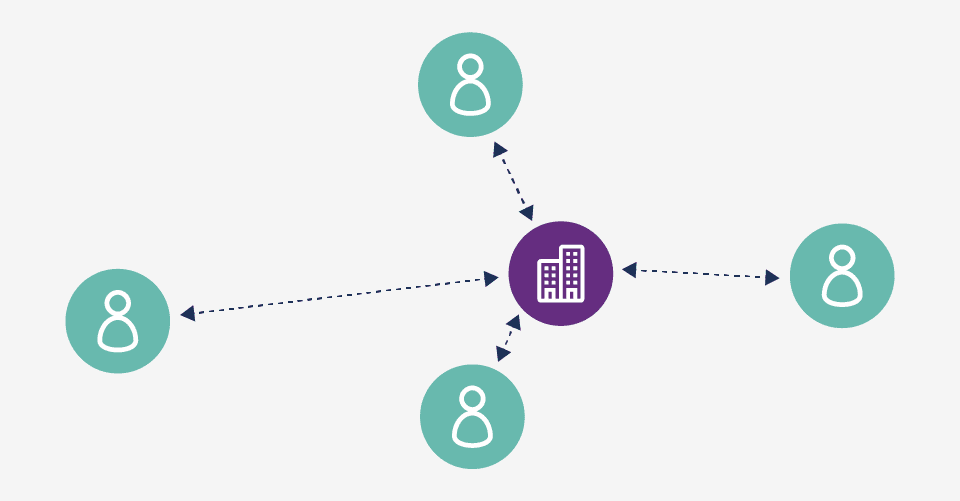
Figure 1: Traditional remote access VPN architecture
Traditionally, VPNs leverage a hub-and-spoke architecture, with users sitting in spokes of various lengths, depend¬ing on their distance from the internal data centre – the ‘hub’ of this analogy. Obviously, the further your employees are from the hub, performance decreases and adds latency challenges too. While this is the optimum solution for data and applications only stored within the hub, the rise in cloud applications, (accessing information via the hub, only to be redirected to the cloud service in question) adds an unnecessary step in the process and can easily overload even the highest bandwidths utilised by large enterprises.
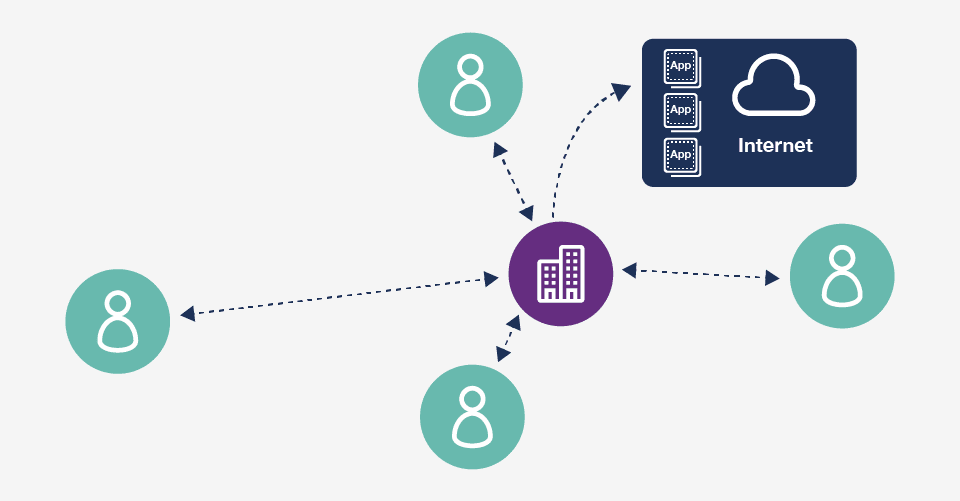
Figure 2: Traditional remote access VPN backhauling traffic to reach the cloud
The causes of this are two-fold. Firstly, when there is a mix of cloud applica¬tions in the environment, traffic must route through the VPN gateway first, even if the application is hosted in the cloud. As a result, the traffic goes to the VPN gateway at headquarters, then from the corporate perimeter firewall to the internet, with the application response going back to headquarters before it returns to the user. Traffic essentially follows a “trombone” path, making a lengthy trip to headquarters to reach a location that is accessible via the internet.
Also, every request must be screened and inspected as it crosses the perimeter firewall, and with most enterprises not having the hardware in place to screen request from so many remote workers, requests start to back-up, causing delays. While this may seem sensible from a security perspective (given that headquarters can inspect the traffic at the hub’s perimeter), it doesn’t make sense in terms of network optimisation.
Unsatisfactory compromises
To compensate for the networking problems with remote access VPN, organisations typically make compromises that have negative security implications.
Some may choose to connect when they need access to the internal data centre and disconnect when they do not, which leads to problems with security policy enforcement. Many cloud service providers leverage encryption, two-factor authentication and other methods of securing data traffic, but when users are not connected via VPN, the enterprise loses visibility into application usage, control over access to unsanctioned applications, and the ability to enforce security policies.
This situation cannot be resolved by adding more VPN gate¬ways. A remote access VPN gateway is simply a termination point for the tunnel, and it does not provide traffic inspection. Even if more VPN gateways were deployed, they would not be able to inspect traffic without additional security measures.
Another common but unsecure method of overcoming the limitations of remote access VPN is to set up a split tunnel. With a split tunnel, traffic bound for the corporate domain goes over the VPN tunnel, and anything else goes directly to the internet. This may reduce latency for internet traffic, but it means there is no traffic inspection at all for internet or cloud traffic.
Considering the rapid growth of remote working, enterprises are finding remote access VPN is neither optimised for the cloud nor secure and a new approach is required to account for today’s application mix. A Modern Architecture for the Mobile Workforce A mobile workforce needs access to the data centre, the internet, and applications across public, private, and hybrid clouds. The right architecture should enable access to all data, with minimised latency, while still ensuring visibility and security, wherever they or the user is located.
Prisma™ Access provides a cloud-delivered security infrastructure that connects users to a nearby cloud gateway, providing secure access to all applications, and maintains full visibility and inspection of traffic across all ports and protocols.
Built for the Mobile Future
Prisma Access connects applications in different locations through its connectivity layer, so users can access all their applications, whether in the cloud or the data centre. The connectivity layer makes it possible to establish secure access— based on App-ID™ and User-ID™ technology policies—to public cloud, software as a service, and data centre applications.
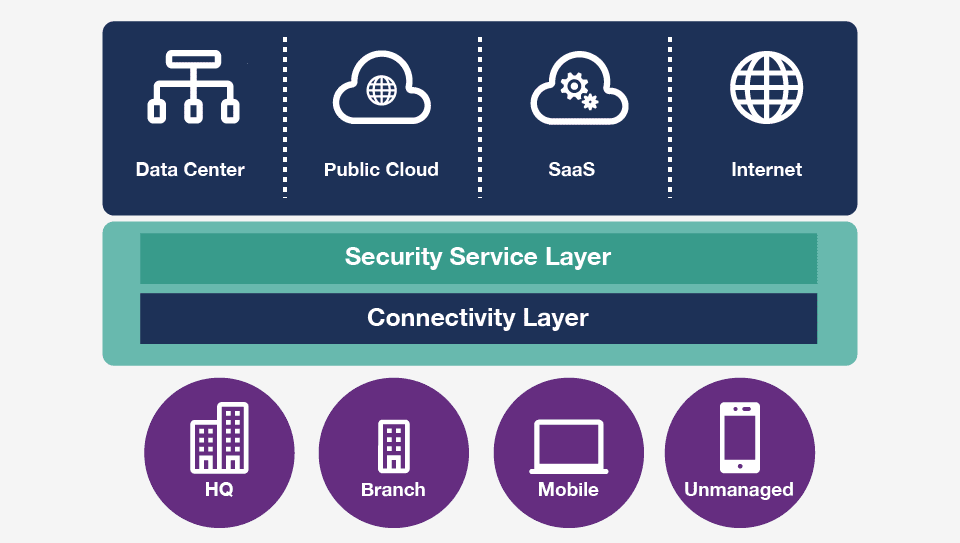
Figure 3: Cloud-delivered protection for all users, no matter where they are
For Managed Mobile Devices
Users’ managed devices—laptops, mobile phones, or tablets—have the GlobalProtect™ app installed. The app automatically connects to Prisma Access whenever internet access is available, without requiring user interaction.
For Unmanaged/BYOD Devices
You can deploy Prisma Access in conjunction with mobile device management (MDM) integration to support the use of bring-your-own-device (BYOD) policies. Integration enables capabilities like per-app VPN. Users with unmanaged devices, such as contractors and employees with BYOD devices, can get remote access to the data center with clientless VPN. This approach enables secure access to SaaS applications from unmanaged devices with in-line protections by using SAML proxy integration.
With Prisma Access, your organisation can overcome the limitations of remote access VPN and support the full spectrum of applications your users need, now and into the future, whatever it holds.
If you’re re-evaluating your remote access VPN deployment, consider BDR. As a Palo Alto partner, we can help you move to an architecture designed for secure access to all applications, while preventing cyberattacks against known and unknown malware exploits, command-and-control traffic, as well as credential-based attacks.

